If unfamiliar, the Cyber Assessment Framework (CAF) is a guide from the UK’s National Cyber Security Centre to help organisations protect themselves from cyber security threats. It’s a valuable resource because it provides a clear, structured way for companies that provide essential services in the UK to assess and improve their cyber security practices, ensuring they are resilient against cyber attacks.
The CAF is split into four primary objectives, with each one having its own set of underlying principles that contribute to fulfilling the objectives. It is highly focused on the “essential function” the organisation provides - for example, generating electricity or providing telecommunications services.
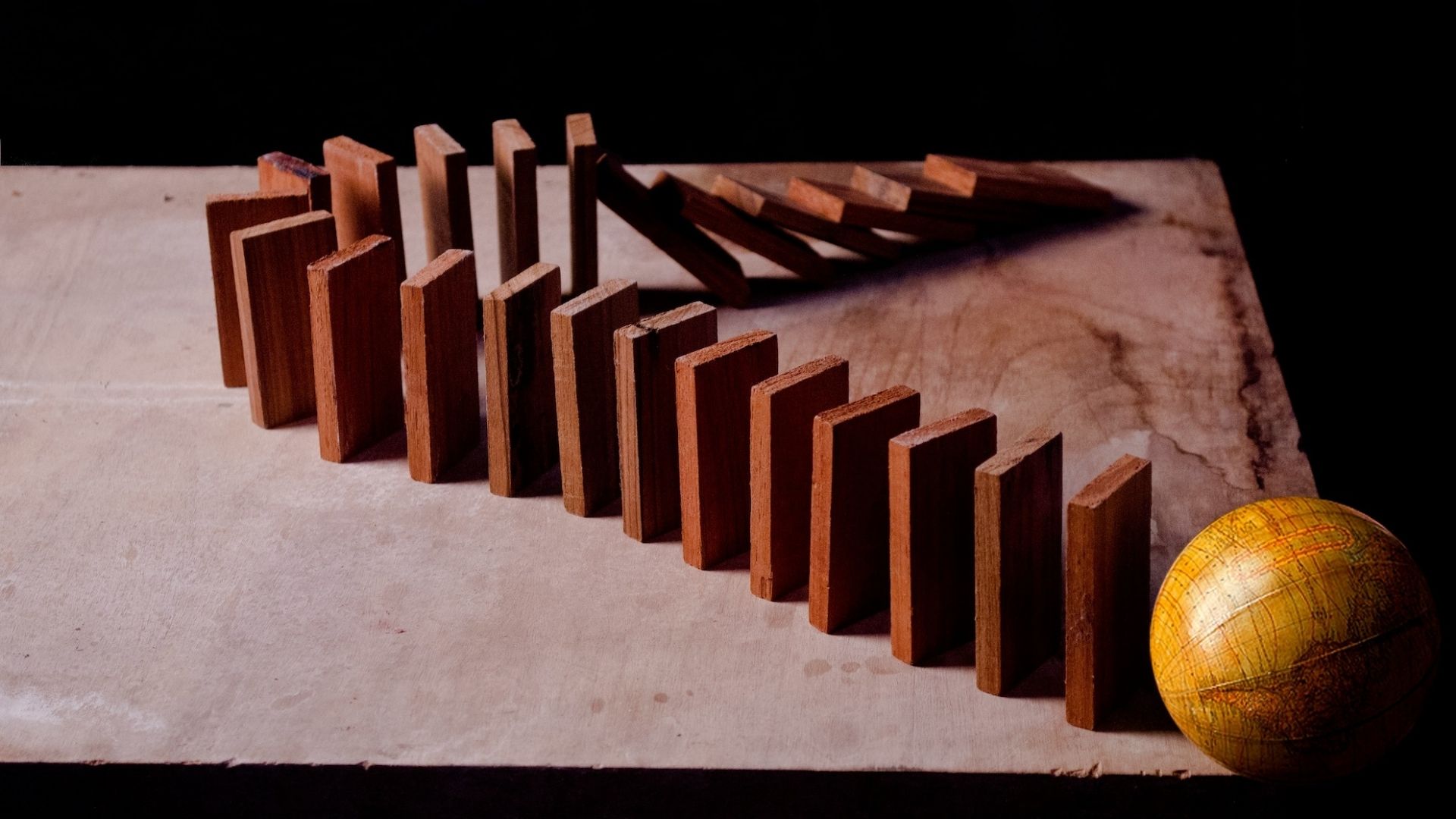
One of the primary objectives is entirely dedicated to managing security risk, showing the importance of a risk-focused approach to cyber security. In this blog post, I’ll explain this objective’s expectations and provide some practical examples of how you can achieve them and what I’ve noticed when helping our customers align to the CAF.
Principle A1 - Governance
“The organisation has appropriate management policies, processes and procedures in place to govern its approach to the security of network and information systems.”
CAF Expectation
Own, manage, and communicate your approach to cyber security at board level, and document it clearly in relevant policies.
Practical Examples
You should regularly discuss cyber security with the board and have a comprehensive suite of policies and standards that inform everyone how to conduct their role with security in mind.
My Tips
I’ve often seen organisations treat cyber security as a purely IT-related issue, without sufficient leadership involvement, which hinders effective risk decision-making. Owning your cyber security approach at board level elevates it to an enabler for success. While this has been a cultural adjustment for some of our customers at first, in the long run it enables them to improve risk dialogue and secure the resources and authority they need to implement an effective security strategy.
CAF Expectation
Define the roles and responsibilities relevant to the security of your network and information systems at all levels, with clear channels in place for communicating and escalating risks.
Practical Examples
You should clearly document who is responsible for patching vulnerabilities on your systems, responding to cyber security incidents, and reviewing current cyber security risks, and how they should do it.
My Tips
Having clear roles and responsibilities is crucial to successfully executing a security strategy. From risk analysis to incident response, clearly documenting and communicating roles and responsibilities ensures everyone is on the same page. For larger organisations with many systems, employees, and suppliers, I’ve seen how tricky it can be to document who is accountable for each security control - it’s worth dedicating some extra time to this part of the process to account for this.
CAF Expectation
Ensure you have senior-level accountability for the security of your network and information systems, and appropriately delegate decision-making authority.
Practical Examples
You should ensure key risks are owned by senior wider business decision-makers (such as members of the executive board) and that they can delegate responsibility to individuals and teams as required to avoid bottlenecks and ensure risks are managed efficiently.
My Tips
When senior leaders take accountability for cyber security and delegate appropriately, it shines a light on crucial risk decisions and gives security teams the authority and executive backing they need to manage risks effectively. Accompanied by the right positive communication, this kind of leadership by example has created a more positive culture for our customers, inspiring others throughout the organisation to be more security-conscious.
CAF Expectation
Consider risks to network and information systems in the context of wider organisational risks.
Practical Examples
You should track your key cyber risks in the same register as other important organisational risks, and ensure they are reviewed by senior leaders to understand their potential impact on the wider business.
My Tips
Viewing cyber threats through the same lens as other major business risks allows you to prioritise security investments based on the actual business impact of potential incidents, and further embeds cyber security into wider business objectives. This has been another cultural adjustment for some customers, which has ultimately led to better risk understanding and accountability for the individuals and teams involved in the risk management process.
Principle A2 - Risk Management
“The organisation takes appropriate steps to identify, assess and understand security risks to network and information systems supporting the operation of essential functions. This includes an overall organisational approach to risk management.”
CAF Expectation
Have effective processes in place to manage and communicate cyber security risks to your essential function.
Practical Examples
You should use a formal, clearly documented process to assess, track, and manage cyber security risks, including communicating them to wider business decision-makers.
My Tips
A structured risk management process turns security from a reactive concern into a predictable and manageable business function. It allows you to consistently address threats before they cause serious disruption to the services your customers rely on. Implementing a formal risk management process has led to greater risk understanding and improved security investment return for our customers. It’s important to define how risks should be communicated with senior leaders to ensure effective decision-making.
CAF Expectation
Understand the current threats you face and use this intelligence to continuously improve your defences.
Practical Examples
You should use relevant threat intelligence and industry reports from respected sources to understand who your adversaries realistically are and feed this information into your risk management process.
My Tips
By understanding your adversaries, you can focus resources on probable and impactful attacks, ensuring your defences match their tactics, capabilities, and motivation. This intelligence-led approach improves security investment return for our customers and enables them to accelerate improvements that meaningfully reduce exposure to key risks. It’s worth considering who will realistically attack your organisation - extremely capable nation-state actors, or far less sophisticated opportunistic criminals?
CAF Expectation
Be confident that your security measures - across your people, processes, and technology - are effective in protecting your essential function.
Practical Examples
You should trust, but verify that your security controls are working as intended through frequent technical tests and compliance audits, and clearly document the results.
My Tips
Confidence shouldn’t be based on assumptions; it must be earned through active testing and validation. For our customers, this assurance proves that their security investments are genuinely reducing exposure to key risks, enabling senior leaders to make informed decisions about their organisation’s true resilience. Documenting test and audit results should not be neglected - if a test is not documented, it’s difficult to prove that it happened.
Principle A3 - Asset Management
“Everything required to deliver, maintain or support networks and information systems necessary for the operation of essential functions is determined and understood. This includes data, people and systems, as well as any supporting infrastructure (such as power or cooling).”
CAF Expectation
Identify and maintain an up-to-date inventory of all assets crucial to your essential function.
Practical Examples
You should have a comprehensive register of all the technology and information assets that are critical to your core business activities and ensure it is actively used, whether in a spreadsheet or a dedicated discovery tool.
My Tips
You can’t protect what you don’t know you have. A complete and current inventory is the foundational map for all security activities, from patching vulnerabilities to responding to an incident. After compiling a detailed asset register, our customers are often surprised at the number of assets or data connections they were unaware of as being relevant to their core business activities.
CAF Expectation
Understand and document the critical infrastructure, like power and cooling, that your essential function depends on.
Practical Examples
You should clearly document the dependencies of your technology and information assets, ideally in the same asset register to create a single source of truth.
My Tips
An attack won’t always target your primary systems directly to make them unavailable - it could instead affect the systems that keep them running. Understanding these dependencies often reveals hidden points of failure to our customers and helps them ensure they are protecting the entire ecosystem their services rely on from both intentional attacks and more traditional hazards.
CAF Expectation
Know which of your assets are the most critical for delivering your essential function.
Practical Examples
You should clearly document the technology and information assets that could have a significant impact on your core business activities if unavailable or compromised, and prioritise them for recovery based on that impact.
My Tips
Prioritising your assets enables you to focus your resources and attention on defending your “crown jewels” - the assets that matter most to keeping your business running and your customers happy. This process often highlights disproportionate security controls and service commitments to our customers, ultimately enabling them to re-prioritise them and achieve a better return on investment.
CAF Expectation
Assign a clear owner responsible for the management and security of every critical asset.
Practical Examples
You should clearly document technology and information asset owners and ensure they understand their responsibilities and feel empowered to carry them out.
My Tips
When an asset has a designated owner, there’s little confusion about who is responsible for its security. This accountability is vital for ensuring that security policies are actually applied. Our customers often appreciate knowing exactly which individual to speak to about a certain asset, leading to improved visibility and compliance tracking. To prevent inefficiencies, it’s important to ensure asset owners have the authority to implement or request changes.
CAF Expectation
Manage security for your critical assets throughout their entire lifecycle, from initial setup to final disposal.
Practical Examples
You should have a documented process used to onboard, maintain, and dispose of critical assets and obtain assurances that the process is followed consistently.
My Tips
An asset can become vulnerable at any point. Managing security across the full lifecycle - from secure configuration at the start to secure data removal at the end - ensures that it is consistently protected. Over time, defining a consistent process to managing and securing assets across their lifecycle reduces misconfigurations and improves compliance tracking for our customers.
Principle A4 - Supply Chain
“The organisation understands and manages security risks to networks and information systems supporting the operation of essential functions that arise as a result of dependencies on suppliers. This includes ensuring that appropriate measures are employed where third party services are used.”
CAF Expectation
Understand and actively manage the security risks that your suppliers introduce to your essential function.
Practical Examples
You should assess the security posture of your critical suppliers and consider the risks they could introduce to your environment as part of your risk management process.
My Tips
Actively managing your supply chain risks is crucial because a vulnerability in a partner’s connected system can become a direct pathway for an attack on your own environment, potentially bypassing key defences. This exercise often highlights previously unknown risks and critical dependencies on supplier services for our customers. It’s important to obtain assurances from suppliers that confirm they are taking security seriously, and looking deeper in the supply chain to fully understand the risks.
CAF Expectation
Prioritise using secure and actively supported software for all your critical systems, whether it’s developed in-house or sourced from a vendor.
Practical Examples
You should document your commitment to minimising the use of unsupported software in relevant policies and have strict criteria for developing or purchasing software to ensure it is upheld.
My Tips
Unsupported software is a ticking time bomb of unpatchable vulnerabilities waiting to be exploited. Using secure and supported software is a fundamental security practice that closes one of the most common avenues of attack. Some critical systems that are no longer supported may be complex to replace - in these cases, it’s important to implement strict compensatory controls to reduce the likelihood of exploitation until an upgrade can be carried out.
Conclusion
In conclusion, a strategic, risk-focused approach, as outlined by the CAF, not only helps protect your essential function but also elevates cyber security as a fundamental enabler of organisational success and resilience.
If you’d like help aligning your cyber risk management process to the CAF, or assessing your risks following its recommendations, get in touch.
Photo by Dushyant Kumar on Unsplash